
18 Maggio 2020
If due to the limitations imposed by the risk of coronavirus contagion you are forced to work from home, don't forget to implement the best IT security procedures to protect against cyber attacks
The surge in coronavirus in this period has created new opportunities for cybercriminals in two different ways. First, through the “coronavirus” topic that has reached search levels unprecedented, giving malicious developers the opportunity to update their toolkits for creating online scams via malicious links and sites based on the search keyword “coronavirus”. Many of the dangers that business users need to watch out for are detailed in our article written by Tony Anscombe of ESET Security, “Beware of scams that exploit the fear of coronavirus."
Therefore, I will focus here on the second method exploited by cybercriminals - the increase in the number of employees working from home and outside the usual, protected corporate networks. In this situation, the attack surface on a company's digital resources is significantly expanded and greater responsibility is required from both employees and management.
Obviously, for some companies the infrastructure and security measures to support employees working from home are already in place, but for others, especially small businesses, this may not be a given. With a few extra precautions, employees of any company can significantly strengthen their digital security posture against a possible attack while working from home.
Here are 5 tips on the best procedures to adopt:
Working from home means that all Internet traffic goes through your home router. Cybercriminals can try to hack into our router, intercepting Wi-Fi traffic and ultimately accessing our network. So, if you haven't looked at your home router setup options, now is the time to do so, before your home network and connected devices are compromised.
Typically, you can access your router's control panel by typing http://192.168.1.1 into your browser while connected to your home network, for example. From there you can change many settings that have a direct impact on security. Be sure to change the default usernames and passwords that come with your router - these can easily be tracked online by a hacker.
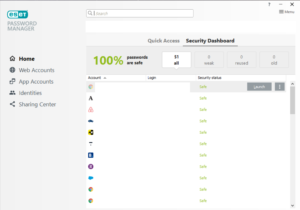
To create strong and unique passwords, we recommend using the ESET Password Manager feature (provided by ESET Smart Security Premium). Using the Password Manager function is ideal because it leads us to remember only one long secret sequence - while all the other passwords for our account come easily with a few clicks via Manager.
It is also useful to change the Service Set Identifier or SSID - which is the name of our home network. By analyzing the SSIDs of the Wi-Fi networks detected by our apartment, we discover that many of our neighbors use Huawei routers - this is free information for an attacker:

We may also use scanning tools to find unwanted devices on our home network. ESET Smart Security Premium, for example, comes with the Connected Home Monitor scan tool that can find rogue neighbors who are perhaps abusively using our Wi-Fi connection without us being informed. It is useful to immediately change our password and eliminate unrecognized devices from the network:

ESET researchers who recently discovered the KrØØk vulnerability in billions of used Wi-Fi chips have verified that for various devices, even in routers, it is essential to ensure that the home router's firmware is updated to the latest version provided by the manufacturer. Finding out that you are using an outdated router means that The time has come to change your home router.
If we need to purchase a new router, we need to evaluate models that can provide greater security for the home network. Some routers, such as those produced by Gryphon, incorporate the features of threat intelligence provided by ESET, which allow you to detect and block malware, phishing sites and other threats on the network for every device connected to your home router.
For more information on home router configuration options, see the blog “How to secure your router to prevent IoT threats”.
Employees who need to access the company's intranet while working remotely will communicate over insecure public networks. You can better protect such communications by using a VPN that establishes a secure channel for communication.
With a VPN, the small data packets that are transmitted can be protected from prying eyes, even while browsing the Internet, allowing them to be decoded only when the data is received, i.e. to employee devices and the company network.
Employees using remote access technologies, such as Remote Desktop Protocol (RDP), are at risk of attacks without adequate security and mitigation options. Threat actors attack RDP with both social engineering employee passwords and forcing login attacks brute-force. In other words, successful attacks against RDP can result from, among other things, mismanagement of the authentication process or social engineering tricks.
Therefore, to better meet authentication needs, companies have the option to use ESET Secure Authentication, ESET's two-factor authentication (2FA) solution, designed to make remote access technologies like VPN and RDP, as well as employee credentials, doubly secure.
The double layer of protection comes from the fact that 2FA requires an employee to enter a one-time code, usually provided via an authentication application (the most secure option), or an SMS, in addition to the usual company username and password. Even if a hacker compromises a password, the presence of 2FA prevents unauthorized access.