ESET, a global leader in the cybersecurity market, has released its Q2 2020 Threat Report highlighting key statistics from its detection systems and showcasing advancements in cybersecurity research, including never-before-seen and exclusive updates.
The report shows how threats related to the COVID-19 pandemic characterized the cybersecurity landscape during the second quarter of 2020.
“ESET telemetry has highlighted a continued influx of COVID-19 recalls in web and email attacks, as well as an increase in targeted Remote Desktop Protocol attacks, with persistent attempts to establish RDP connections more than doubling since the start of the year,” commented Roman Kováč, Chief Research Officer at ESET.
The Q2 2020 Threat Report examined the most important areas of study and major achievements of ESET researchers. For example, the analysis of a ramsonware attack targeting Canadian Android users disguised as an anti-Covid tracking app – “We quickly put an end to this operation and provided a solution for the victims” underlines Roman Kováč.
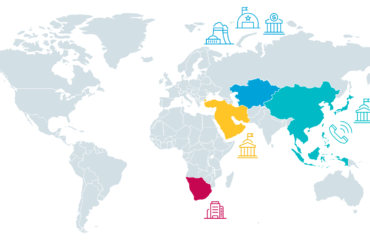
Among the many findings obtained, ESET researchers discovered Operation In(ter)ception, which targeted high-profile aerospace and military companies; revealed the modus operandi of the infamous InvisiMole group; and analyzed Ramsay, a cyberespionage toolkit specifically for air-gapped networks.
Some of the exclusive research presented in the Report includes malicious Google Chrome extensions targeting cryptocurrency hardware wallets, a new attack on Hong Kong University by the Winnti group, as well as additional Operation In(ter)ception-related attacks against military organizations in Brazil, the Czech Republic, Qatar, Turkey and Ukraine.
In addition to these findings, the ESET Q2 2020 Threat Report provides a summary of the company's contributions to the MITER ATT&CK knowledge base, as well as the participation of ESET experts in upcoming conferences and workshops.
Learn more at this link