The goal is to steal sensitive data and spy on victims' messaging apps
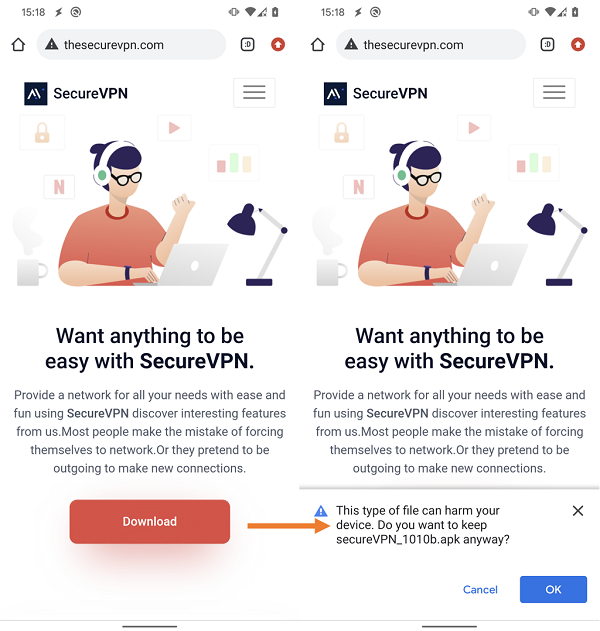
Researchers of ESET, a global leader in the cybersecurity market, have identified a campaign running from early 2022, aimed at Android users, led by the APT Bahamut group. Spyware applications are distributed through a fake SecureVPN website that only offers Android apps containing trojans for download. This website has no relation to the legitimate SecureVPN cross-platform software and service. The apps used are capable of exfiltrating contacts, SMS messages, recorded phone calls and even chat messages from apps such as WhatsApp, Facebook Messenger, Signal, Viber and Telegram. ESET has discovered at least eight versions of the Bahamut spyware, confirming that the campaign is well fueled. Malicious apps were never available for download from Google Play.
"The data exfiltration occurs via the keylogging functionality of the malware, which illicitly uses accessibility services. The campaign is specifically targeted, since no cases are detected in the telemetry data -, he explains Lukáš Štefanko, ESET researcher which discovered and analyzed Android malware. – Additionally, the application requires an activation key to enable VPN and spyware features. Both the activation key and the website link are likely sent to targeted users." The layer is intended to protect the malicious payload from being activated immediately after launch on a device of a user not targeted or being analyzed. ESET Research has already observed the use of this type of protection in another campaign by the Bahamut group.
All exfiltrated data is stored in a local database and then sent to the Command and Control (C&C) server. The functionality of the Bahamut spyware includes the ability to update the app via a link to a new version from the C&C server.
If the spyware is enabled, it can be remotely controlled by Bahamut operators and can exfiltrate various sensitive device data, such as contacts, SMS, call logs, list of installed apps, device location, account and device information (internet connection type, IMEI, IP, SIM serial number), recorded phone calls and list of files present in external storage. By abusing Accessibility Services, malware can steal notes from the SafeNotes app and spy on chat and call information from popular messaging apps.
The APT Bahamut group uses spearphishing messages and bogus applications as an initial attack vector, against organizations and individuals in the Middle East and South Asia. Bahamut specializes in cyberespionage and ESET Research believes his goal is to steal sensitive information from victims. Bahamut is also believed to be a mercenary group that offers paid hacking services to a large number of customers. The name for this group was chosen by the investigative journalism team Bellingcat who was inspired by the enormous fish that roams the Arabian Sea mentioned in the Book of imaginary beings by Jorge Luis Borges.
Further technical information on the latest campaign of the APT Bahamut group, in this in-depth analysis "Bahamut cybermercenary group targets Android users with fake VPN apps” su WeLiveSecurity.