ESET Research has analyzed social engineering campaigns based on fake job interviews and the ClickFix technique, linked to North Korean IT workers involved in fraudulent hiring practices and cryptocurrency theft, presented in a new white paper
Researchers of ESET, a global European leader in the cybersecurity market, have released new findings on DeceptiveDevelopment, also known as Contagious Interview: a North Korea-aligned threat group that has intensified its activities in recent years. The group has as its main objective the theft of cryptocurrencies and targets freelance developers on Windows, Linux and macOS.
The new white paper reconstructs the evolution of the group, from the first malware to more advanced toolsets. The identified campaigns rely on particularly ingenious social engineering techniques, such as fake job interviews and ClickFix, a methodology that leads victims to execute malicious commands under the guise of solving technical problems, allowing attackers to distribute malware and exfiltrate cryptocurrency. In parallel, ESET analyzed open-source intelligence (OSINT) data linking North Korean IT operators, perpetrators of fraudulent hiring practices, to the DeceptiveDevelopment group. The findings were presented at the annual Virus Bulletin (VB) conference.
Active since at least 2023, DeceptiveDevelopment is a group aligned with North Korea addicted to theft of cryptocurrencies. It affects software developers operating on all major operating systems – Windows, Linux and macOS – with a particular focus on cryptocurrency and Web3 projects. Initial access is gained through social engineering techniques, including ClickFix and the use of fake recruiter profiles, similar to those already employed by the Lazarus group in the DreamJob operation, by which code packages containing Trojans are distributed during simulated interviews. The most recurring payloads are the infostealers BeaverTail, OtterCookie and WeaselStore, as well as the modular backdoor InvisibleFerret RAT.
"The operators of DeceptiveDevelopment use fake recruiter profiles on social media, similar to the Lazarus Group's DreamJob operation. In this case, however, they specifically target software developers, often involved in crypto projects, by providing them with code packages containing Trojans that install backdoors as part of a fake selection process," explains Peter Kálnai, co-author of the white paper. "The actors behind these operations give up extreme technical sophistication in favor of large-scale operations and very creative social engineering. Their malware is relatively simple, but they still manage to target even experienced targets," adds Kálnai.
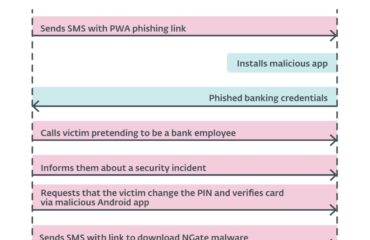
Attackers use various methods to compromise victims, using social engineering techniques. Through fake or compromised profiles, they pose as recruiters on platforms such as LinkedIn, Upwork, Freelancer.com and Crypto Jobs List, offering attractive job offers. Victims are asked to complete a programming challenge or pre-interview task.
In addition to fake profiles, attackers have adapted and perfected the ClickFix technique. Victims are directed to a fake interview site and asked to fill out a detailed form, which takes time and energy. At the end of the process, they are asked to record a video response, but the site shows a camera error and offers a “How to fix” link. Following the instructions, victims open a terminal and copy a command that, instead of solving the supposed problem, downloads and executes malware on the device.
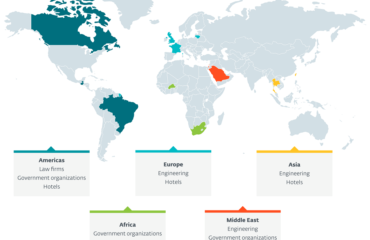
Although the study on DeceptiveDevelopment is based mainly on ESET telemetry data and technical analysis of the group's toolset, links emerge with fraudulent operations conducted by North Korean IT operators. According to the FBI, this campaign has been active since at least 2017 and has become increasingly relevant. In a joint statement from May 2022 it is described as an operation coordinated by operators aligned with North Korea to obtain jobs in foreign companies, with salaries intended to finance the regime. Additionally, in a January 2025 announcement, the FBI reported cases of theft of internal company data, which was later used for extortion.
From the analysis of OSINT data, fake CVs and other materials, ESET Research found that these operators are mainly targeting the US market, but recently the focus has also shifted to Europe, with targets in France, Poland, Ukraine and Albania. These profiles use AI to carry out work tasks, manipulate photos for CVs and profiles, and even perform real-time face swaps during video interviews, taking on the appearance of the identity used. They leverage platforms such as Zoom, MiroTalk, FreeConference and Microsoft Teams to carry out various social engineering techniques. Proxy interviewing represents a significant risk for companies, as hiring illegitimate staff from sanctioned countries can not only reduce performance, but can also result in a serious internal threat.
"The activities of North Korean IT operators constitute a hybrid threat. This fraudulent commission scheme combines classic criminal practices, such as identity theft and the creation of synthetic identities, with digital tools, placing it halfway between traditional crime and cybercrime," observes Kálnai.
The white paper “DeceptiveDevelopment: From primitive crypto theft to sophisticated AI-based deception” traces the evolution of the group's two main toolsets, InvisibleFerret and BeaverTail. It also highlights links between the Tropidoor backdoor and the PostNapTea RAT, already used by the Lazarus group. It also analyzes in detail TsunamiKit and WeaselStore, the new DeceptiveDevelopment toolkits, documenting the operation of a C&C WeaselStore server and the related API.