From mid-2020, ESET, a global leader in the cybersecurity market, analyzed multiple malicious initiatives, later attributed to cyber espionage group Gelsemium, and traced back to the first version of their main malware, Gelsevirine, from 2014.
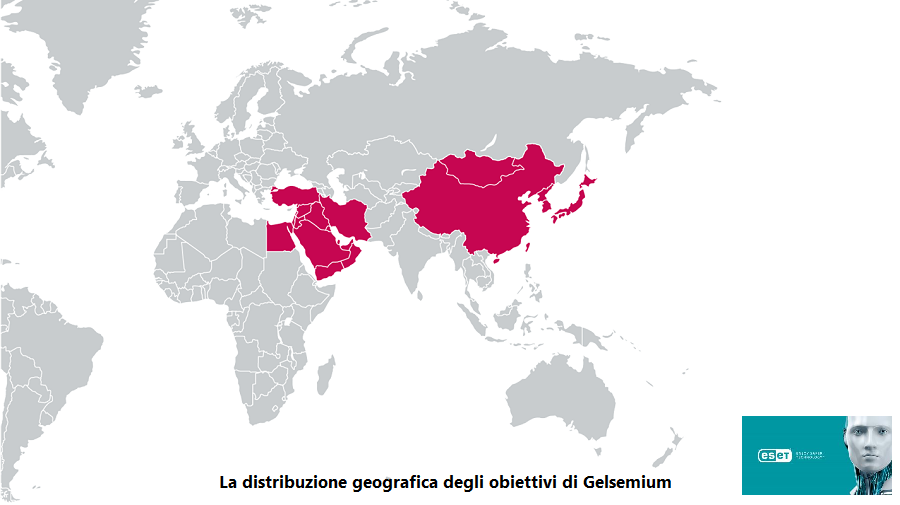
During the investigation, ESET researchers discovered a new version of Gelsevirine, a complex and modular backdoor. Victims of its campaigns are found in East Asia and the Middle East and include government organizations, religious organizations, electronics manufacturers and universities. At the moment, the group has managed to operate without attracting too much attention. The research was exclusively previewed at the ESET World annual conference this week.
Gelsemium is a very specific malware - with a limited number of victims, according to ESET's telemetry - but considering its potential, the group is believed to be involved in cyber espionage. The group has a large number of adaptable components. "The entire chain of Gelsemium might seem simple at first glance, but the exhaustive number of configurations, implanted in each phase, can change the final payload settings in an instant, making it more difficult to grasp," he explains Thomas Dupuy, ESET Researcher and co-author of the research analysis on Gelsemium.
Gelsemium uses three components and a plug-in system to give users a range of information gathering possibilities: the Gelsemine dropper, the Gelsenicine loader and the main Gelsevirine plugin.
ESET researchers believe Gelsemium is responsible for the supply chain attack against BigNox, previously reported by ESET as Operation NightScout. It was a supply-chain attack, which compromised the update mechanism of NoxPlayer, an Android emulator for PC and Mac, and part of the BigNox product range, with over 150 million users worldwide. The investigation found a certain similarity between this attack and the Gelsemium group. The victims originally compromised by the supply-chain attack were subsequently violated by Gelsemine. Among the different variants examined, the "variant 2" illustrated in this article shows similarities with the Gelsemium malware.
More technical details on Gelsemium, in the blogpost "Gelsemium: when threats go shopping”On WeLiveSecurity. All the latest news can be found by following ESET Research su Twitter.






